The error I experienced
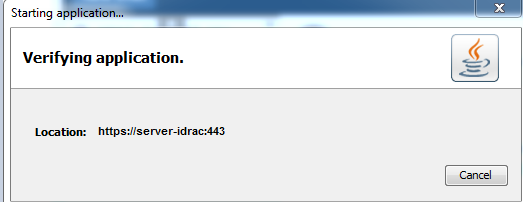
When connecting to iDRAC , you may experience a timeout:
- using proxy configured via pac script
- which is downloaded over HTTPS
- using the Java plugin (or using Native, but a non Internet Explorer browser where ActiveX is unsupported – it will revert to Java)
It hangs for about 60 seconds in the state Verifying Application
When you click the “Launch Console” link/button in the iDRAC web interface, a token is generated and stored in the .jnlp file you subsequently download. This allows you to open the .jnlp in the javaws client without re-authenticating with the iDRAC.
This token is valid for about 90 seconds, before it expires.
If :
- you are unable to answer the (many many) security prompts AND
- wait for the application (.jar files etc) to be downloaded AND
- for the connection verified (e.g. Certificates validated),
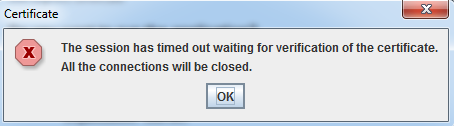
within 90 seconds, the token will expire and you will need to connect again. You will see an error such as
The session has timed out waiting for verification of the certificate. All the connections will be closed
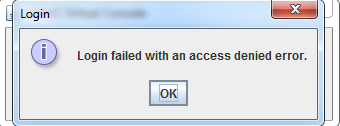
Or
Login failed with an access denied error
Java logs (showing connection attempt)
Note 15 seconds delay between attempting to connect to ocsp.verisign.com and the timeout being reached. This occurred several times before it eventually gave up and proceeded anyway
<record>
<date>2016-10-18T10:15:25</date>
<millis>1476746125541</millis>
<sequence>306</sequence>
<logger>com.sun.deploy</logger>
<level>FINE</level>
<class>com.sun.deploy.trace.LoggerTraceListener</class>
<method>print</method>
<thread>8</thread>
<message>network: Connecting socket://ocsp.verisign.com:80 with proxy=DIRECT
</message>
</record>
<record>
<date>2016-10-18T10:15:40</date>
<millis>1476746140468</millis>
<sequence>307</sequence>
<logger>com.sun.deploy</logger>
<level>FINE</level>
<class>com.sun.deploy.trace.LoggerTraceListener</class>
<method>print</method>
<thread>8</thread>
<message>security: Failing over to CRLs: java.net.SocketTimeoutException: connect timed out
</message>
</record>
Observations/Learnings
- Java by default uses the “browser settings” for proxy config
- If using a proxy automatic configuration (pac) script, it will
- Download the script
- Evaluate the proxy settings
- When downloading the proxy script over HTTPS, it evaluates the cert. As the server hosting the proxy script is generated using a non-public CA, whose certs aren’t automatically distributed.
- If Java mixed code signing verification is enabled, it attempts to connect to ocsp.verisign.com:80 to verify the certificate signature.
- At this stage, because the proxy script hasn’t yet been downloaded, it is unable to figure out how to connect to verisign, so it attempts a direct connection.
- After multiple connection attempts, this eventually (after ~60 seconds) times out
- The proxy automatic configuration script is now downloaded, and the Dell iDRAC certificate signature is verified using the appropriate proxy path defined in the .pac file.
How to work around the fault
- Disable mixed code signing verification in Java options
- Hard set the proxy either in Global Internet Options (e.g. Internet Explorer) or in the Java options
- Host the pac script on a server accessible using HTTP (not secured)
- Allow direct internet access from your client system to ocsp.verisign.com
- Newer Dell iDRACs support HTML5 - use this
- Try using the native iDRAC console plugin with Internet Explore (ActiveX) - this also has security implications.
None of these actually resolve the underlying Java client fault that it requires a pac file to be applied so that it can retrieve the pac file.